Baiting
Baiting lives in the same vein as phishing; it is when a social engineer plants a malicious object, hoping someone will activate it. When they do so, it may install malware, track activity, gain access to personal information, or even manipulate what is typed on your computer!
What to watch for:
A social engineer will leave a malicious flash drive, in hopes someone will connect it to their personal or work computer.
Found a phone charger? Not so fast!
New tools allow social engineers to embed tracking devices into phone USB cables that look like genuine ones, for both iPhones and Androids.
Though it may be tempting, you shouldn’t use any charging cables that you find in a public place.
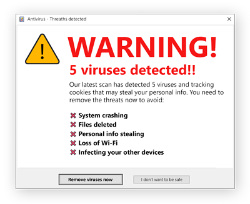
False “virus detected” messages may appear when browsing the internet. They are a kind of bait; even though they are digital, they still want you to click so they can infiltrate your device. If you see one, close that website immediately, and check your actual antivirus program if you’d like. As long as you didn’t click the popup, there should be no issues.
As QR codes become more widespread, social engineers have begun to exploit them. Before opening the links associated with any QR code, make sure you know that it leads to a legitimate website.

